Checkout our website for prospective students.
Dr. Alekseyev Receives NSF Career Award
 Dr. Alekseyev has received the National Science Foundation's CAREER award. The Faculty Early Career Development (CAREER) Program is NSF's most prestigious award in support of the early career-development activities of junior faculty.
The award supports his research on developing software and algorithms to aid in the reconstruction of ancestral genomes and the construction of an evolutionary history of genomes.
The full title of the award is CAREER: PRUGC---Phylogenetic Reconstructions with Unequal Gene Contents. The project abstract follows:
Dr. Alekseyev has received the National Science Foundation's CAREER award. The Faculty Early Career Development (CAREER) Program is NSF's most prestigious award in support of the early career-development activities of junior faculty.
The award supports his research on developing software and algorithms to aid in the reconstruction of ancestral genomes and the construction of an evolutionary history of genomes.
The full title of the award is CAREER: PRUGC---Phylogenetic Reconstructions with Unequal Gene Contents. The project abstract follows:
The proposed project "PRUGC—Phylogenetic Reconstructions with Unequal Gene Contents" addresses the problem of reconstruction of ancestral genomes and evolutionary history of genomes that may deviate in gene content, resulting from genome rearrangements as well as gene duplications and deletions evolutionary events. It will close the gap between steadily growing number of sequenced genomes and incapability of existing phylogenetic reconstruction tools to process diverse varieties of genomes. Similarly to the previous phylogenetic reconstruction tool MGRA developed by the PI, the new PRUGC software will employ the framework of multiple breakpoint graphs that will be extended to address new algorithmic challenges arising from genomes having unequal gene contents. As some of these challenges may be hard and have no computationally feasible solutions, instead of focusing on a fixed evolutionary model and attempting to fit biological problems into it, the PI will let the model be flexible and problem-driven. In the course of PRUGC development, the PI plans to address the following particularly important biological problems (listed in the order of growing complexity): the primate-rodent-carnivore split controversy in mammalian evolution (featuring relatively small number of duplications); phylogenetic analysis of a diverse variety of yeast genomes including genomes that undergone whole genome duplications; and evolutionary problems in plant evolution rich in segmental duplications. Solutions to these problems will help to better understand the mechanisms behind chromosome evolution across variety of genomes. The reconstructed ancestral genomes will provide insights to functional significance of particular gene orders, help to rigorously estimate the rate of genome rearrangements and gene duplications/deletions in different organisms, and allow testing hypotheses about their mechanisms and influence on shaping genomic architectures. It is important to emphasize that the PRUGC software will have a wide range of applications, not limited to the aforementioned problems. Other immediate applications will arrive from a number of the PI's collaborative projects, such as analysis of rearrangements in malaria mosquito genomes (a joint project with Dr. Igor Sharakhov from Virginia Tech University). The PRUGC software will also be helpful in various phylogenomic studies within projects like "Tree of Life", "Genome 10K", and "i5k". It will be released as both a standalone open-source tool and an online web-server application readily accessible for use by biologists. The project will support research activities in the PI's research lab. In particular, it will help to prepare a new generation of researchers in bioinformatics by providing the opportunities to have hands-on experiences in both computer science and biology. One undergraduate student and two Ph.D. students will be recruited with the support of this project, and the PI will mentor these students and prepare them for building their careers in academia or industry. The PI will make every effort to help the students gain first-hand experience of biology, including short-term visits to our local, national, and international collaborators. Such experience will also help the students to develop and enhance their ability to communicate with researchers in other areas, an important skill in interdisciplinary research. The project will also offer an excellent opportunity for computer science students to learn about experimental and theoretical research in the interdisciplinary area of bioinformatics. Detailed explanation of the whole process of multiple genomes comparison will perfectly fit into a timeframe of a bioinformatics course. The PI plans to lecture this material within the bioinformatics course CSCE 555 offered for undergraduate and graduate students at the University of South Carolina. As a member of the Bioinformatics Education Alliance developing "Bioinformatics for Biologists" (B4B) textbook, the PI coordinated with the editors preparation of a new chapter module and web-based educational materials for the next edition of B4B that will expand the current chapter on genome rearrangements and illustrate their applications with a number of biological problems within the PRUGC project.The NSF CAREER program recognizes and supports the early career-development activities of those teacher-scholars who are most likely to become the academic leaders of the 21st century. CAREER awardees are selected on the basis of creative career-development plans that effectively integrate research and education within the context of the mission of their institution and department.
Supporting Computer Science in South Carolina
 Dr. Buell has been awarded an NSF grant to help students across South Carolina learn about Computer Science and the many opportunities the field offers. As part of this grant, the Expanding Computing Education Pathways Alliance and the University of South Carolina (Columbia) will collaborate to build state-based infrastructures to improve and support computer science in South Carolina.
This will include promoting ECEP summer camp seed funding opportunities and train-the-trainers workshops; seeking opportunities to draw upon the Experts Bureau and NCWIT resources to inform policy-makers and other education leaders; and furthering the development and broadening of computing education pathways in South Carolina.
Dr. Buell has been awarded an NSF grant to help students across South Carolina learn about Computer Science and the many opportunities the field offers. As part of this grant, the Expanding Computing Education Pathways Alliance and the University of South Carolina (Columbia) will collaborate to build state-based infrastructures to improve and support computer science in South Carolina.
This will include promoting ECEP summer camp seed funding opportunities and train-the-trainers workshops; seeking opportunities to draw upon the Experts Bureau and NCWIT resources to inform policy-makers and other education leaders; and furthering the development and broadening of computing education pathways in South Carolina.

Hood and DeBruin win Magellan Scholarship

 Two of our undergraduate students received Magellan Scholar awards. Logan Hood received an award for his project on "Affordable Medical Ultrasound Training Simulator" and Garret DeBruin for his project titled "Classification and Detection of Proteotypic Peptides Through The Use of Hidden Markov Models and Neural Networks." Congratulations to both of them!
Garret DeBruin's project abstract:
Two of our undergraduate students received Magellan Scholar awards. Logan Hood received an award for his project on "Affordable Medical Ultrasound Training Simulator" and Garret DeBruin for his project titled "Classification and Detection of Proteotypic Peptides Through The Use of Hidden Markov Models and Neural Networks." Congratulations to both of them!
Garret DeBruin's project abstract:
Classification and Detection of Proteotypic Peptides Through The Use of Hidden Markov Models and Neural Networks In traditional peptide sequencing an unknown peptide’s MSMS spectrum is used as a query to a database. This query yields a set of peptides with spectra similar to the observed spectrum. A more difficult problem is De Novo peptide sequencing, which does not depend on a database of known peptides. De Novo peptide sequencing has the problem of considering all possible peptides consistent with the observed spectrum, and ranking them according to some scoring function. Proteotypic peptides are peptides that are easily fragmented by collision induced dissociation and are easily detected by tandem mass spectrometers. In contrast, nonproteotypic peptides are unlikely to be detected. Under the proposed approach, it would be possible to improve de novo sequencing results by discounting nonproeotypic peptides since they are unlikely to be detected even though they are consistent with the observed spectrum. This would significantly improve the accuracy of the sequencing.
JJ Shepherd at TEDxColumbiaSC
 Our very own JJ Shepherd will be giving a talk at TEDxColumbiaSC 2013, in January. The talk is titled "How video games should be taken seriously as a research field, a rehabilitation aid and an art form". In this USC News article JJ says:
Our very own JJ Shepherd will be giving a talk at TEDxColumbiaSC 2013, in January. The talk is titled "How video games should be taken seriously as a research field, a rehabilitation aid and an art form". In this USC News article JJ says:
I want to give this talk to spread the message that games are not just a ‘kid’s toy,’ but are a unique medium that combines art and science into one artifact. These artifacts can not only entertain, but also teach us, train us and evoke new ideas that no other medium has ever been able to do.
Wireless Snooping on Electric Meters
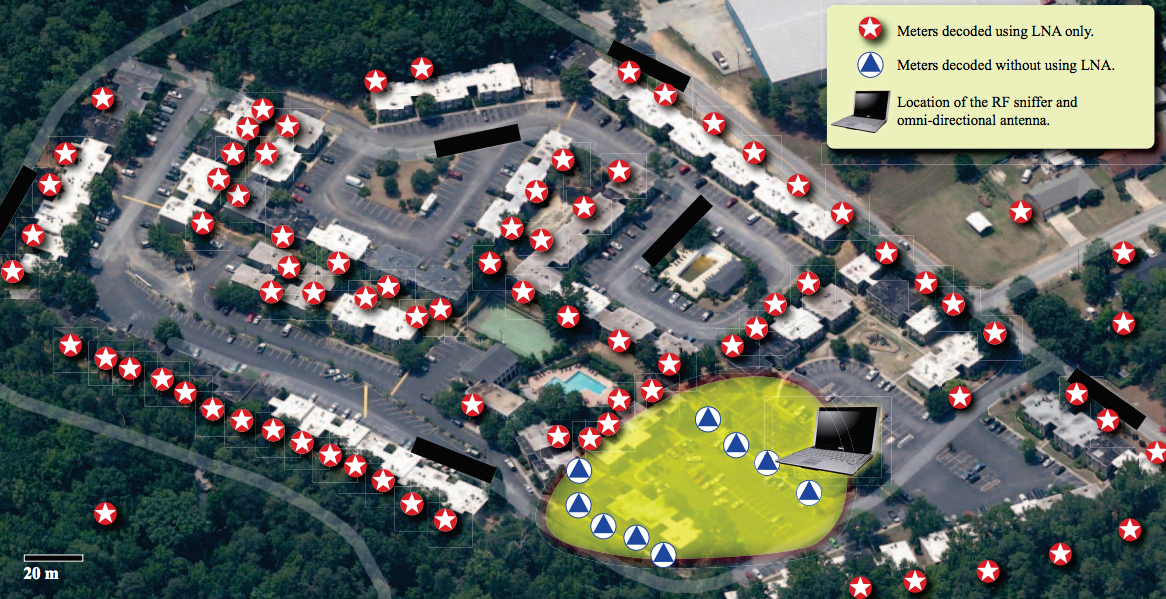 MIT's Technology Review covers Dr. Wenyuan Xu's research on snooping on electric meters in their article Another Reason for "Smart" Electric Meters.
MIT's Technology Review covers Dr. Wenyuan Xu's research on snooping on electric meters in their article Another Reason for "Smart" Electric Meters.
Researchers from the University of South Carolina discovered that they could read meter signals at a 400-unit housing complex in such detail they could determine that 27 units were unoccupied. And because the meters send out data every 30 seconds, the researchers could infer some residents' daily habits by spotting sudden jumps in electricity usage. In their paper, the researchers wrote that in one unit in the complex, "the owners got up at 7 a.m., left for work at 9 a.m., and returned home around 6 p.m. on Friday."WISTV has picked up the story: WIS Investigation: students test security of utility's Automatic Meter Reading. You can watch the video online. These research results were published in a paper at the ACM Conference on Computer and Communications Security.
 You can read the full paper: Neighborhood Watch: Security and Privacy Analysis of Automatic Meter Reading Systems where they provide all the details of this research.
Our own USC Times also covers this story in their article Is your utility meter getting personal?.
You can read the full paper: Neighborhood Watch: Security and Privacy Analysis of Automatic Meter Reading Systems where they provide all the details of this research.
Our own USC Times also covers this story in their article Is your utility meter getting personal?.
Lead researcher Wenyuan Xu, a professor in USC’s College of Engineering and Computing, says that much of the focus in the research security community right now is on the next generation of devices, the so-called “smart” meters. Utilities hope in the future they will be able to use these smart meters to match electricity flow to individual houses with overall demand, enabling much more efficient allocation of resources.The Industrial Safety and Security Source picks it up in Smart Meters Need to Get Smarter. Computerworld: Some smart electricity meters are stupid about privacy. The University main page: White Knight: USC researcher hacks for good.

NSF Funds Mobile Technology for Perioperative Services
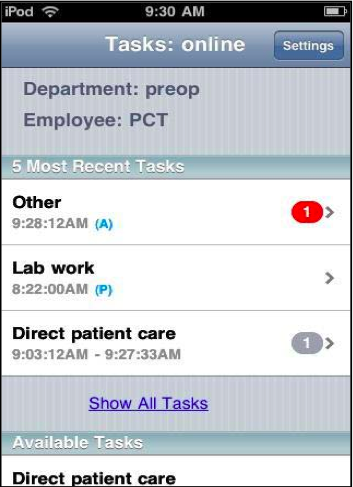 Dr. Nathan Huynh and Dr. Jose M Vidal have received $600K from the National Science Foundation (NSF) for research on mobile technology for use in hospitals, as part of a $1.4M grant shared with colleagues from Clemson University. The goal of the research is to determine how mobile technology can best be used to improve coordination in a hospital's perioperative services. The researchers will develop and test a mobile app that will include speech recognition, natural language processing, and other artificial intelligence techniques in order to deliver the right information at the right time to hospital staff, and to recommend tasks that should be handled next.
Research trials will be carried out at three hospitals: Greenville Memorial Hospital, Palmetto Health Richland in the Columbia area and the Medical University of South Carolina in Charleston.
You can also see Clemson's press release or the official NSF Award page.
Proposal Abstract
This project proposes to create a framework using a combination of mobile technology, learning systems, data analytics, education, and training to enhance cooperation and coordination of staff within and across perioperative services departments (POS). Perioperative services comprise surgery preparation, operating rooms, post-anesthesia care, sterile processing and a variety of other services, such as radiology and endoscopy. The specific objectives of this project are to: (1) enhance communication and coordination among POS staff to improve the quality of care by gathering and using important workflow milestones and introducing artificial intelligence techniques through the use of a smart-app, (2) analyze workflow data gathered with smart-apps using data analytics to provide intuitive displays of real-time information for frontline staff and a daily performance dashboard for managers, and (3) induce behavioral and cultural change in healthcare systems through training and education. While existing information technology capabilities such as natural language processing, artificial intelligence, and speech recognition technology are promising developments in computing, their uses in health care are limited and thus need to be thoroughly investigated before they can be used in health care effectively. To accomplish these objectives, the research team will work closely with the partnering healthcare organizations, Greenville Hospital System (GHS), Palmetto Health (Palmetto), and the Medical University of South Carolina (MUSC), in developing the tools and models which will be pilot-tested at these organizations by their staff.
The developed tools and models will be widely disseminated among health care providers in South Carolina. In addition, the smart-apps and agent-based simulation model will provide the team with a teaching and training tool that can be used in the classroom at Clemson University and the University of South Carolina (USC) to teach students across a variety of fields, such as business, engineering, science and healthcare students about information and workflow management techniques.
Dr. Nathan Huynh and Dr. Jose M Vidal have received $600K from the National Science Foundation (NSF) for research on mobile technology for use in hospitals, as part of a $1.4M grant shared with colleagues from Clemson University. The goal of the research is to determine how mobile technology can best be used to improve coordination in a hospital's perioperative services. The researchers will develop and test a mobile app that will include speech recognition, natural language processing, and other artificial intelligence techniques in order to deliver the right information at the right time to hospital staff, and to recommend tasks that should be handled next.
Research trials will be carried out at three hospitals: Greenville Memorial Hospital, Palmetto Health Richland in the Columbia area and the Medical University of South Carolina in Charleston.
You can also see Clemson's press release or the official NSF Award page.
Proposal Abstract
This project proposes to create a framework using a combination of mobile technology, learning systems, data analytics, education, and training to enhance cooperation and coordination of staff within and across perioperative services departments (POS). Perioperative services comprise surgery preparation, operating rooms, post-anesthesia care, sterile processing and a variety of other services, such as radiology and endoscopy. The specific objectives of this project are to: (1) enhance communication and coordination among POS staff to improve the quality of care by gathering and using important workflow milestones and introducing artificial intelligence techniques through the use of a smart-app, (2) analyze workflow data gathered with smart-apps using data analytics to provide intuitive displays of real-time information for frontline staff and a daily performance dashboard for managers, and (3) induce behavioral and cultural change in healthcare systems through training and education. While existing information technology capabilities such as natural language processing, artificial intelligence, and speech recognition technology are promising developments in computing, their uses in health care are limited and thus need to be thoroughly investigated before they can be used in health care effectively. To accomplish these objectives, the research team will work closely with the partnering healthcare organizations, Greenville Hospital System (GHS), Palmetto Health (Palmetto), and the Medical University of South Carolina (MUSC), in developing the tools and models which will be pilot-tested at these organizations by their staff.
The developed tools and models will be widely disseminated among health care providers in South Carolina. In addition, the smart-apps and agent-based simulation model will provide the team with a teaching and training tool that can be used in the classroom at Clemson University and the University of South Carolina (USC) to teach students across a variety of fields, such as business, engineering, science and healthcare students about information and workflow management techniques.Undergraduate Scholarship Winner
 Mr. Andrey Gavel has been awarded a 2012 UPE Special Recognition Scholarship Award from Upsilon Pi Epsilon, the Computing Sciences Honor Society. This is a nice honor. It is a national competition held once a year and open to all Computer Science undergraduate and graduate majors. You can view the official list of winners for this year.
Mr. Andrey Gavel has been awarded a 2012 UPE Special Recognition Scholarship Award from Upsilon Pi Epsilon, the Computing Sciences Honor Society. This is a nice honor. It is a national competition held once a year and open to all Computer Science undergraduate and graduate majors. You can view the official list of winners for this year.
Gamecock Computing Symposium Award Winners

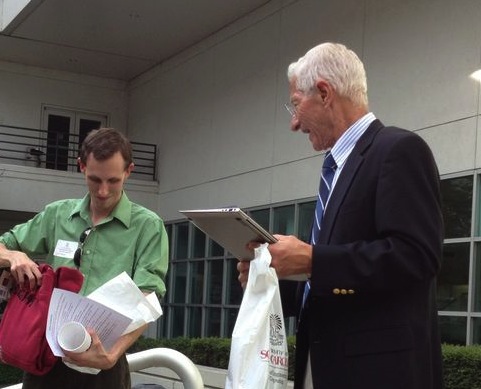 Our first Gamecock Computing Research Symposium was a major success. We had over 40 research posters. All who attended had very positive things to say about it and other departments are already thinking about copying us, if they can! If you do not already follow our Twitter feed (also posted on this page, right column) then you might have missed this photo album, taken by Prof. Nelakuditi or this one, by me.
Most importantly, we want to congratulate Mr. Jarrell Waggoner and Mr. Nicholas Stiffler for winning the poster awards! Both shown here receiving their awards from Dr. Huhns.
Our first Gamecock Computing Research Symposium was a major success. We had over 40 research posters. All who attended had very positive things to say about it and other departments are already thinking about copying us, if they can! If you do not already follow our Twitter feed (also posted on this page, right column) then you might have missed this photo album, taken by Prof. Nelakuditi or this one, by me.
Most importantly, we want to congratulate Mr. Jarrell Waggoner and Mr. Nicholas Stiffler for winning the poster awards! Both shown here receiving their awards from Dr. Huhns.
Robots Helping Children with Autism
Laura Boccanfuso, one of our graduate students, is featured on this WISTV news story along with her robot Charlie:


Charlie is short for Child Centered Adaptive Robot for Learning Environments, designed by a USC graduate student to help kids with autism. "She is designed to promote basic communication skills," said Charlie creator Laura Boccanfuso. "Two of the most important communication skills are imitation and turn taking." Charlie is designed to be handled by kids but sometimes kids play hard, which is why she has some break away features. "We want the robot to just be sitting on a table, and allow the child to explore her, touch the eyes, touch the nose, and the hands and get to know her so she and he feels comfortable interacting with the robot," said Boccanfuso.Full story at WISTV.com. The College of Engineering coverage of this story. medGaget blog coverage. USC News coverage.
Genome3D: Exploring the Genome in a Computer
Prof. Jijun Tang and colleagues at MUSC have received a grant from the NSF for their collaborative research on "Developing a 3D Browser to Explore Genomes". This project builds upon the success of the Genome3D and leverages recent findings on complex spatial genomic models. Exploring genomes through 3D visualization will significantly advance genome research in integrating epigenomic data, studying long range inter- and intra-chromosome interaction, and analyzing structural features of genetic variations. Check it out on the video below.
Digital Image Analysis Research Grant
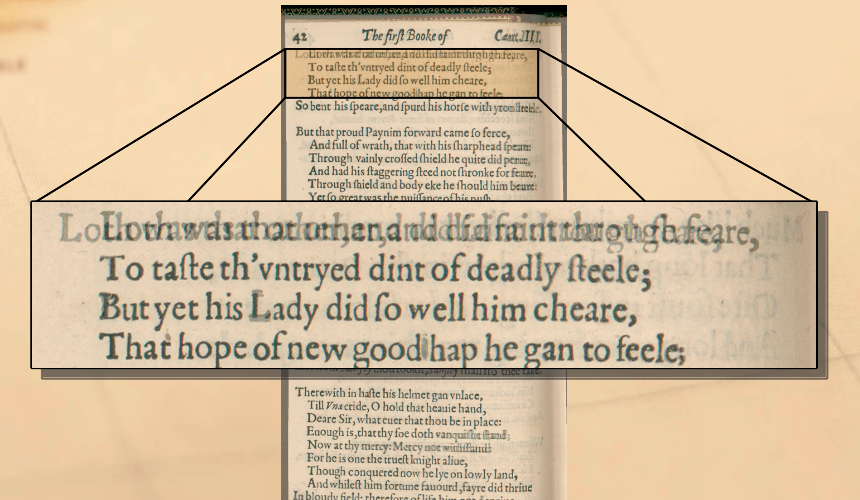 Together with Prof. David Miller from the Center for Digital Humanities, Prof. Song Wang has been awarded a research grant from National Endowment for the Humanities (NEH) for their project "PARAGON: Intelligent Digital Collation and Difference Detection." In this project, they will develop new image processing algorithms and open-source software to automate the detailed comparison of scanned images captured under varying circumstances, whether scanned, camera-taken from different heights or angles, rotated, differently lighted, or even slightly warped. This research will substantially reduce the intensive labor that is currently required in the study of print materials and facilitate the digitalization of rare and fragile historical documents.
The USC News has an article on the Center for Digital Humanities that mentions this research.
Together with Prof. David Miller from the Center for Digital Humanities, Prof. Song Wang has been awarded a research grant from National Endowment for the Humanities (NEH) for their project "PARAGON: Intelligent Digital Collation and Difference Detection." In this project, they will develop new image processing algorithms and open-source software to automate the detailed comparison of scanned images captured under varying circumstances, whether scanned, camera-taken from different heights or angles, rotated, differently lighted, or even slightly warped. This research will substantially reduce the intensive labor that is currently required in the study of print materials and facilitate the digitalization of rare and fragile historical documents.
The USC News has an article on the Center for Digital Humanities that mentions this research.Student Receives Palmetto Pillar Award
 We are pleased to announce that Mr. Nicholas Stiffler, a graduate student in Computer Science and Engineering, has won the 2012 Palmetto Pillar Award in the category of Student Achievement. This is a statewide award that is given annually by the Greater Columbia Chamber of Commerce and the Information Technology Council (ITC) and honors the best and brightest of the Midlands technology community. Congratulations!
We are pleased to announce that Mr. Nicholas Stiffler, a graduate student in Computer Science and Engineering, has won the 2012 Palmetto Pillar Award in the category of Student Achievement. This is a statewide award that is given annually by the Greater Columbia Chamber of Commerce and the Information Technology Council (ITC) and honors the best and brightest of the Midlands technology community. Congratulations!New Faculty: Prof. Matt Thatcher
 We are happy to welcome Dr. Matt E. Thatcher our newest Professor. He comes here from the University of Lousville where he was a Professor of Computer Information Systems. Before that, he was an Associate Professor of Management Information Systems at the University of Nevada, Las Vegas and an Assistant Professor of Management Information Systems at the University of Arizona. He received his Ph.D. in Information Systems at The Wharton School, University of Pennsylvania. His research interests are in IT value, software patent policy design, IT offshoring, and the social costs of information privacy.
His office is in Swearingen 3A58 and he will be teaching 190: Computing in the Modern World and 390: Professional Issues in Computer Science and Engineering this Fall.
We are happy to welcome Dr. Matt E. Thatcher our newest Professor. He comes here from the University of Lousville where he was a Professor of Computer Information Systems. Before that, he was an Associate Professor of Management Information Systems at the University of Nevada, Las Vegas and an Assistant Professor of Management Information Systems at the University of Arizona. He received his Ph.D. in Information Systems at The Wharton School, University of Pennsylvania. His research interests are in IT value, software patent policy design, IT offshoring, and the social costs of information privacy.
His office is in Swearingen 3A58 and he will be teaching 190: Computing in the Modern World and 390: Professional Issues in Computer Science and Engineering this Fall.Computational Biology Research Grants
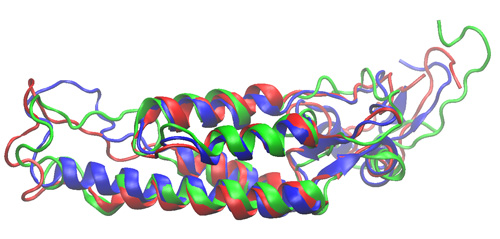 Our Computational Biology Research lab, headed by Dr. Valafar, has received two separate research grants for continued support of their work. The first one is for their ongoing project on the "South Carolina IDeA Network of Biomedical Research Excellence (INBRE)", funded by National Institute of General Medical Sciences (NIGMS)/NIH. The second award comes to Dr. Stephanie Irausquin, a Research Scientist in the lab, in the form of a National Science Foundation fellowship for her project titled "A Novel RDC Analysis Pipeline for Determination of Protein Structure and Dynamics."
Our Computational Biology Research lab, headed by Dr. Valafar, has received two separate research grants for continued support of their work. The first one is for their ongoing project on the "South Carolina IDeA Network of Biomedical Research Excellence (INBRE)", funded by National Institute of General Medical Sciences (NIGMS)/NIH. The second award comes to Dr. Stephanie Irausquin, a Research Scientist in the lab, in the form of a National Science Foundation fellowship for her project titled "A Novel RDC Analysis Pipeline for Determination of Protein Structure and Dynamics."52apps: Another Student Startup
 52apps is a new company formed by some of our students that is building one new app every week based on users' ideas. They appeared on the local news tonight. Check our their homepage every week to see what new app they built this week, and lend them your support.
52apps is a new company formed by some of our students that is building one new app every week based on users' ideas. They appeared on the local news tonight. Check our their homepage every week to see what new app they built this week, and lend them your support.